45 Minutes. $440 Million. Gone.
It starts fast.
Orders firing. Systems flooding. Dashboards spike in ways no one’s seen before.
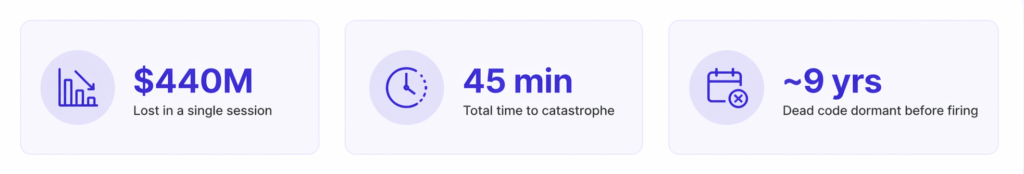
$440M lost in 45 minutes due to legacy code
At Knight Capital Group, engineers are staring at screens that don’t make sense. Trades are executing but not the right ones. The system isn’t failing. It’s doing exactly what it’s told.
45 minutes. That’s all it took for a rogue algorithm to execute four million unintended trades.
Not a cyberattack. No obvious crash. No system outage. Just a failure of Release Intelligence.
This is what the Knight Capital bug actually looked like in real time.
The Real Cause: The dead code trap
The trigger wasn’t some exotic bug. It was old, forgotten code.
A dormant function tied to the SMARS algorithm, written years earlier, accidentally reactivated during a deployment. It had been sitting there since 2003. Untouched and unmonitored.
According to SEC findings, a deployment inconsistency caused this legacy logic to run in production. Not everywhere. Just enough to cause chaos.
Knight Capital’s team wasn’t negligent. They ran tests. They reviewed the new feature. Their CI/CD pipeline was green. By every traditional metric, this was a clean release. The problem wasn’t the code they checked — it was the system they didn’t understand.
That’s your Enterprise Dark Matter. Enterprise Dark Matter is the unseen system-level risk that exists outside your defined test coverage — in dependencies, legacy paths, and unexpected interactions.
You don’t see it. You don’t test for it. But it’s there. And it’s waiting.
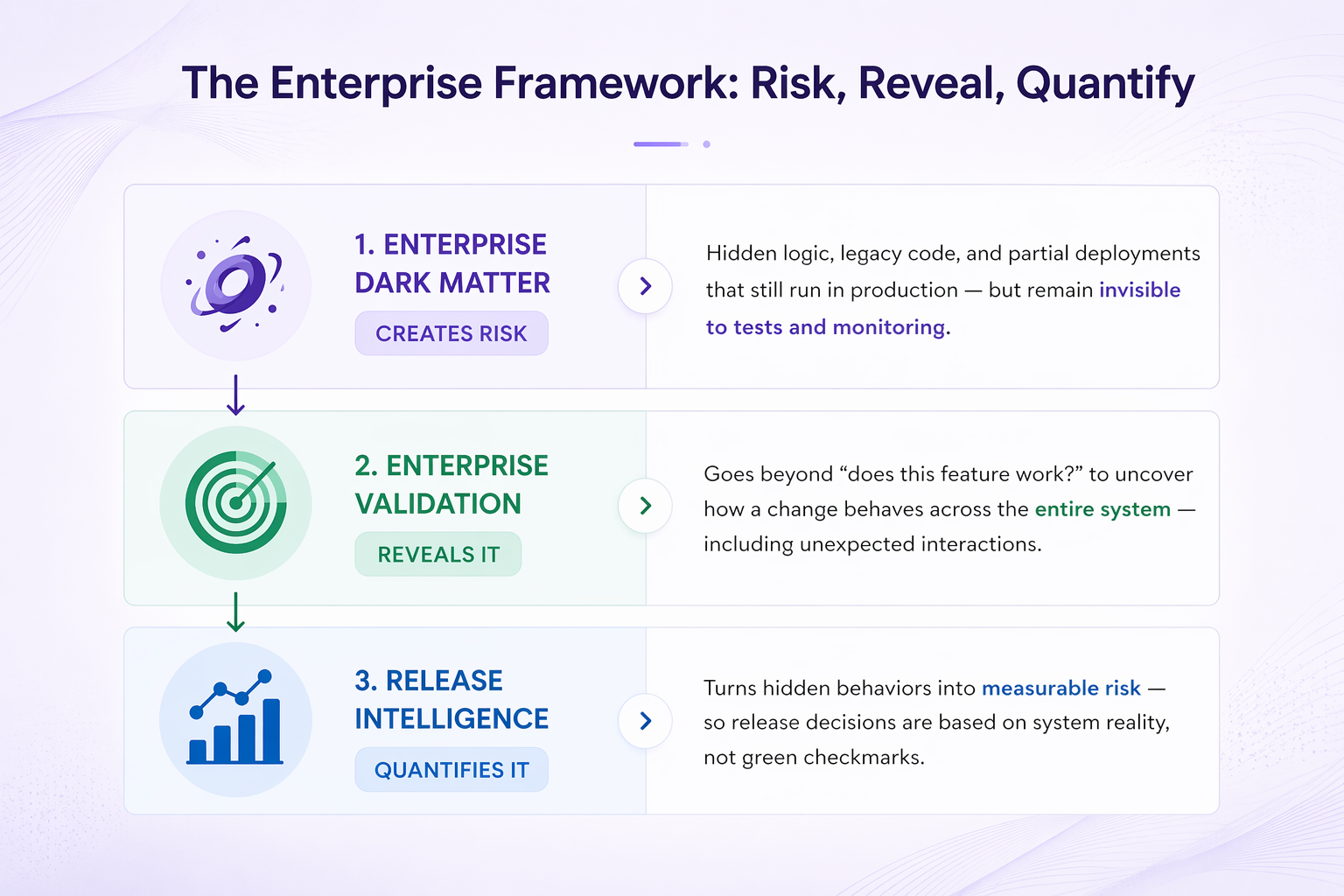
Risk creation, validation, and quantification model
Why your test automation didn’t catch this
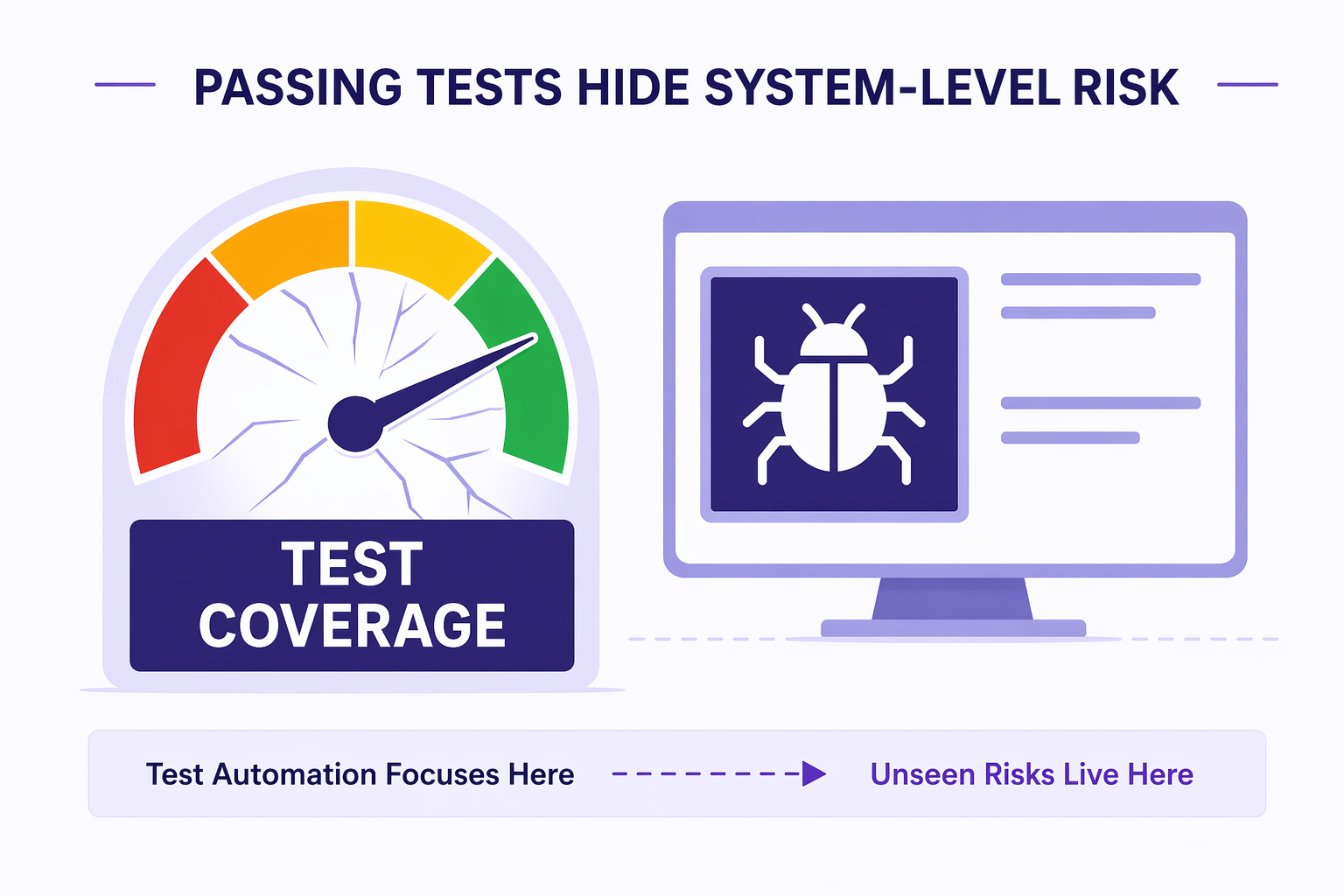
Passing tests don’t reveal system-level failures
Your green checkmark is not a release guarantee. It’s a narrow confirmation. It tells you one thing: the scenarios you defined passed.
It tells you nothing about everything else your system is doing.
Traditional automation is fundamentally limited:
- Linear: It checks expected outputs for known inputs
- Atomic: It validates components in isolation
- Reactive: It only catches what you explicitly told it to look for
That worked when systems were simple. It breaks in a system-of-systems environment.
Because you’re no longer managing a codebase. You’re managing an ecosystem.
Every deployment doesn’t just add code. It disturbs an existing state. Dependencies shift. Timing changes. Old paths get reactivated.
And your tests? They’re still looking in the same places.
Key lessons for the modern CTO
- Legacy Is a Liability: Technical debt risk isn’t just slow code. It’s a dormant execution risk waiting for the right trigger.
- Complexity Doesn’t Scale Linearly: Every deployment expands your system’s state space. Not by a little but exponentially.
- Testing Isn’t Validation: Testing asks, “Does this work?” Validation asks, “What did this change across the system?”
Related Reading: Why traditional software quality strategies fail in modern enterprise systems
The Shift to Enterprise Validation and Release Intelligence
To survive, you need to move beyond testing.
Release Intelligence is the difference between a fingers-crossed deployment and a controlled, observable change.
It answers the questions your pipeline doesn’t:
- What changed across the system?
- Which dependencies were impacted?
- Where is risk now concentrated?
Because in modern B2B SaaS infrastructure, a release isn’t an update. It’s a system-wide event.
Enterprise Validation starts where your test suite ends. Passing unit tests aren’t dismissed — they’re the baseline. What happens next is what matters.
It extends beyond defined test cases into actual system behavior:
- Tracks state changes across services
- Identifies unexpected interactions between components
- Surfaces triggers in legacy or dormant code paths
A clear view of how your system is reacting in real time.
Stop treating releases like a gamble
The CTO who learned the wrong lesson from Knight Capital Group built a better test suite.
The CTO who learned the right lesson extended visibility into the system itself – building Release Intelligence into the release process.
Because execution of tests isn’t the finish line. It’s where understanding begins.
Stop treating deployments as green checkmarks.
Start treating every release as a validated system-wide change — one that accounts for what you expect, what you missed, and what’s still quietly running underneath.
Because that’s where the real risk lives. The $440 million ghost was never random. It was already in the system.
The only question is whether you see it before it executes.
Aquila brings Release Intelligence into your pipeline, so every deployment is a validated systemic change. Schedule a personalized demo to learn more.
Frequently Asked Questions (FAQ)
What was the Knight Capital bug?
The Knight Capital bug was a production failure where a dormant piece of legacy code was unintentionally triggered during deployment, leading to millions of unintended trades and a $440 million loss within 45 minutes.
Why did the Knight Capital bug happen despite testing?
Because traditional test automation validated expected scenarios, not the full system behavior. The failure came from an untested interaction between new deployment changes and dormant legacy code.
Can test automation prevent production failures like this?
Not entirely. Test automation can catch known issues, but it cannot detect unknown interactions or hidden risks across complex systems. That requires system-level validation and Release Intelligence.
What is Release Intelligence in software delivery?
Release Intelligence is the ability to understand how a code change impacts the entire system, including dependencies, legacy components, and real-world workflows, before it reaches production.